CVE-2026-33626
LMDeploy Vulnerable to Server-Side Request Forgery (SSRF) via Vision-Language Image Loading
Description
LMDeploy is a toolkit for compressing, deploying, and serving large language models. Versions prior to 0.12.3 have a Server-Side Request Forgery (SSRF) vulnerability in LMDeploy's vision-language module. The `load_image()` function in `lmdeploy/vl/utils.py` fetches arbitrary URLs without validating internal/private IP addresses, allowing attackers to access cloud metadata services, internal networks, and sensitive resources. Version 0.12.3 patches the issue.
INFO
Published Date :
April 20, 2026, 9:16 p.m.
Last Modified :
April 23, 2026, 1:39 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Update LMDeploy to version 0.12.3 or later.
- Validate image URLs before loading them.
- Restrict access to internal network resources.
Public PoC/Exploit Available at Github
CVE-2026-33626 has a 6 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2026-33626.
| URL | Resource |
|---|---|
| https://github.com/InternLM/lmdeploy/commit/71d64a339edb901e9005358e0633fbbab367d626 | Patch |
| https://github.com/InternLM/lmdeploy/pull/4447 | Issue Tracking Patch |
| https://github.com/InternLM/lmdeploy/releases/tag/v0.12.3 | Release Notes |
| https://github.com/InternLM/lmdeploy/security/advisories/GHSA-6w67-hwm5-92mq | Exploit Mitigation Vendor Advisory |
| https://github.com/InternLM/lmdeploy/security/advisories/GHSA-6w67-hwm5-92mq | Exploit Mitigation Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2026-33626 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2026-33626
weaknesses.
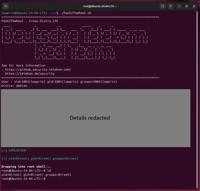
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Curadoria viva de projetos e insights sobre AI agents, multi-agent systems, e infra de produção. Atualizado automaticamente pelo Growth Agent.
None
HTML Handlebars Shell C C++ Go Java JavaScript PHP Python
Experimentation
Python Batchfile VBScript PowerShell
An AI-Powered Vulnerability Impact Agent
Python Shell HTML
Automated daily recon for everything new in cybersecurity. Scans 50+ sources every 24 hours.
bugbounty cve-tracker cybersecurity cybersecurity-news cybersecurity-tools exploit-development offensive-security pentesting red-team threat-intelligence
None
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-33626 vulnerability anywhere in the article.

-
The Hacker News
cPanel, WHM Release Fixes for Three New Vulnerabilities — Patch Now
Ravie LakshmananMay 09, 2026Vulnerability / Web Hosting cPanel has released updates to address three vulnerabilities in cPanel and Web Host Manager (WHM) that could be exploited to achieve privilege ... Read more

-
The Hacker News
Linux Kernel Dirty Frag LPE Exploit Enables Root Access Across Major Distributions
Details have emerged about a new, unpatched local privilege escalation (LPE) vulnerability impacting the Linux kernel. Dubbed Dirty Frag, it has been described as a successor to Copy Fail (CVE-2026-31 ... Read more

-
The Hacker News
Ivanti EPMM CVE-2026-6973 RCE Under Active Exploitation Grants Admin-Level Access
Ivanti is warning that a new security flaw impacting Endpoint Manager Mobile (EPMM) has been explored in limited attacks in the wild. The high-severity vulnerability, CVE-2026-6973 (CVSS score: 7.2), ... Read more

-
The Hacker News
PCPJack Credential Stealer Exploits 5 CVEs to Spread Worm-Like Across Cloud Systems
Cybersecurity researchers have disclosed details of a new credential theft framework dubbed PCPJack that targets exposed cloud infrastructure and ousts any artifacts linked to TeamPCP from the environ ... Read more

-
The Hacker News
PAN-OS RCE Exploit Under Active Use Enabling Root Access and Espionage
Palo Alto Networks has disclosed that threat actors may have attempted to unsuccessfully exploit a recently disclosed critical security flaw as early as April 9, 2026. The vulnerability in question is ... Read more

-
The Hacker News
ThreatsDay Bulletin: Edge Plaintext Passwords, ICS 0-Days, Patch-or-Die Alerts and 25+ New Stories
Bad week.Turns out the easiest way to get hacked in 2026 is still the same old garbage: shady packages, fake apps, forgotten DNS junk, scam ads, and stolen logins getting dumped into Discord channels ... Read more

-
The Hacker News
Critical Apache HTTP/2 Flaw (CVE-2026-23918) Enables DoS and Potential RCE
The Apache Software Foundation (ASF) has released security updates to address several security vulnerabilities in the HTTP Server, including a severe vulnerability that could potentially lead to remot ... Read more

-
The Hacker News
MetInfo CMS CVE-2026-29014 Exploited for Remote Code Execution Attacks
Threat actors are actively exploiting a critical security flaw impacting an open-source content management system (CMS) known as MetInfo, according to new findings from VulnCheck. The vulnerability in ... Read more

-
The Hacker News
Weaver E-cology RCE Flaw CVE-2026-22679 Actively Exploited via Debug API
A critical security vulnerability in Weaver (Fanwei) E-cology, an enterprise office automation (OA) and collaboration platform, has come under active exploitation in the wild. The vulnerability (CVE-2 ... Read more

-
The Hacker News
Progress Patches Critical MOVEit Automation Bug Enabling Authentication Bypass
Progress Software has released updates to address two security flaws in MOVEit Automation, including a critical bug that could result in an authentication bypass. MOVEit Automation (formerly Central) ... Read more

-
The Hacker News
CISA Adds Actively Exploited Linux Root Access Bug CVE-2026-31431 to KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a recently disclosed security flaw impacting various Linux distributions to its Known Exploited Vulnerabilities (KEV) c ... Read more

-
The Hacker News
China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists
Cybersecurity researchers have disclosed details of a new China-aligned espionage campaign targeting government and defense sectors across South, East, and Southeast Asia, along with one European gove ... Read more

-
The Hacker News
New Linux 'Copy Fail' Vulnerability Enables Root Access on Major Distributions
Cybersecurity researchers have disclosed details of a Linux local privilege escalation (LPE) flaw that could allow an unprivileged local user to obtain root. The high-severity vulnerability tracked as ... Read more

-
The Hacker News
Google Fixes CVSS 10 Gemini CLI CI RCE and Cursor Flaws Enable Code Execution
Google has addressed a maximum severity security flaw in Gemini CLI -- the "@google/gemini-cli" npm package and the "google-github-actions/run-gemini-cli" GitHub Actions workflow -- that could have al ... Read more

-
The Hacker News
LMDeploy CVE-2026-33626 Flaw Exploited Within 13 Hours of Disclosure
A high-severity security flaw in LMDeploy, an open-source toolkit for compressing, deploying, and serving LLMs, has come under active exploitation in the wild less than 13 hours after its public discl ... Read more

-
Daily CyberSecurity
Critical 9.8 CVSS Flaws Hit ArcGIS Infrastructure
Esri has issued an urgent security bulletin regarding two critical vulnerabilities affecting developer credentials within ArcGIS Online, ArcGIS Location Platform, and ArcGIS Enterprise. The flaws, whi ... Read more

-
Daily CyberSecurity
In the Wild: Information Disclosure (CVE-2026-20133) Exploited in Cisco SD-WAN Manager
The networking giant Cisco has issued an urgent warning to enterprise administrators. In April 2026, the Cisco Product Security Incident Response Team (PSIRT) confirmed they are aware of active exploi ... Read more
-
Daily CyberSecurity
Linux Privilege Escalation: “Pack2TheRoot” Flaw Impacts Major Distributions
A long-standing security flaw has been unearthed in a core component of the modern Linux desktop and server ecosystem. Known as Pack2TheRoot, this critical vulnerability resides in PackageKit, a D-Bus ... Read more

-
Daily CyberSecurity
Over 400,000 WordPress Sites at Risk as “Breeze” Plugin Zero-Day Is Exploited in the Wild
A major security threat is currently sweeping through the WordPress ecosystem. Breeze, a highly popular caching plugin developed by the Cloudways team and active on over 400,000 websites, is under act ... Read more

-
Daily CyberSecurity
CVE-2026-33626: High-Severity SSRF Exploited in the Wild to Hijack AI Inference Engines
On April 21, 2026, a high-severity Server-Side Request Forgery (SSRF) vulnerability was disclosed in LMDeploy, a popular toolkit for serving vision-language and large language models (LLMs). Within a ... Read more
The following table lists the changes that have been made to the
CVE-2026-33626 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Apr. 23, 2026
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:internlm:lmdeploy:*:*:*:*:*:*:*:* versions up to (excluding) 0.12.3 Added Reference Type GitHub, Inc.: https://github.com/InternLM/lmdeploy/commit/71d64a339edb901e9005358e0633fbbab367d626 Types: Patch Added Reference Type GitHub, Inc.: https://github.com/InternLM/lmdeploy/pull/4447 Types: Issue Tracking, Patch Added Reference Type GitHub, Inc.: https://github.com/InternLM/lmdeploy/releases/tag/v0.12.3 Types: Release Notes Added Reference Type CISA-ADP: https://github.com/InternLM/lmdeploy/security/advisories/GHSA-6w67-hwm5-92mq Types: Exploit, Mitigation, Vendor Advisory Added Reference Type GitHub, Inc.: https://github.com/InternLM/lmdeploy/security/advisories/GHSA-6w67-hwm5-92mq Types: Exploit, Mitigation, Vendor Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Apr. 21, 2026
Action Type Old Value New Value Added Reference https://github.com/InternLM/lmdeploy/security/advisories/GHSA-6w67-hwm5-92mq -
New CVE Received by [email protected]
Apr. 20, 2026
Action Type Old Value New Value Added Description LMDeploy is a toolkit for compressing, deploying, and serving large language models. Versions prior to 0.12.3 have a Server-Side Request Forgery (SSRF) vulnerability in LMDeploy's vision-language module. The `load_image()` function in `lmdeploy/vl/utils.py` fetches arbitrary URLs without validating internal/private IP addresses, allowing attackers to access cloud metadata services, internal networks, and sensitive resources. Version 0.12.3 patches the issue. Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N Added CWE CWE-918 Added Reference https://github.com/InternLM/lmdeploy/commit/71d64a339edb901e9005358e0633fbbab367d626 Added Reference https://github.com/InternLM/lmdeploy/pull/4447 Added Reference https://github.com/InternLM/lmdeploy/releases/tag/v0.12.3 Added Reference https://github.com/InternLM/lmdeploy/security/advisories/GHSA-6w67-hwm5-92mq